防火長城
中国大陆的互联网审查系统 来自维基百科,自由的百科全书
防火長城[1](英語:Great Firewall,GFW),中國國家防火牆[2],或簡稱為牆、防火牆[3]等,中國網信辦稱其為數據跨境安全網關[註 1][4][5],是中華人民共和國政府用以過濾互聯網出口內容的軟硬件系統集合。防火長城不是中國特有的一個專門單位,而是由分散部門的各伺服器和路由器等裝置,加上相關公司的應用程式構成,其監控所有經過國際閘道器的通訊,對認為不符合中國官方要求的傳輸內容,進行干擾、阻斷、封鎖。由於中國網絡審查廣泛,中國大陸內含有「不合適」內容的網站,會受到政府直接的行政干預,故防火長城主要作用在於分析和過濾中國境外網絡的資訊。自本世紀初以來,防火長城由國家電腦網絡與資訊保安管理中心(CNCERT)運營和維護[6][7][8]。
隨着防火長城逐漸為人熟知,「牆」一詞有時也被用作動詞[9],「被牆」即指網站內容被防火長城所封鎖[10][11],「翻牆」也被引申為突破網絡審查瀏覽中國大陸境外被封鎖的網站或使用服務的行為。
歷史
中國1994年接入互聯網[12],1995年被中國稱為「互聯網年」[13][14]。
中國政府對互聯網的管控始於1996年,總理李鵬簽署了國務院令第195號,發佈施行《電腦資訊網絡國際聯網管理暫行規定》。其中第六條規定:「電腦資訊網絡直接進行國際聯網,必須使用郵電部國家公用電信網提供的國際出入口信道。任何單位和個人不得自行建立或者使用其他信道進行國際聯網」。該規定在後來被廣泛用於處罰「翻牆」行為[15][16]。
最早使用Great Firewall一詞的是白傑明和桑曄,他們1997年發表的文章《The Great Firewall of China》稱這一系統開發開始在1996年,並且當年在金橋資訊網和ChinaNet已經有國外新聞網站被封鎖[14]。
技術手段方面,一開始防火長城僅使用IP封鎖,這並不能應對網站時常更換IP的情況[17][18]。自2002年開始,其能夠自動執行針對特定域名的DNS劫持,並能夠檢測HTTP連接中的特定關鍵字,使用TCP重設攻擊的方法阻止連接[17][19]。
自2010年以來,HTTPS(加密的HTTP)開始被廣泛使用,維基媒體計劃也於2015年切換到僅加密連接[20],而防火長城在很長一段時間內都沒有處理加密連接。直到2018年8月,對加密連接中「伺服器名稱指示」(SNI)資訊的檢測才出現,而此時正是關於加密伺服器名稱指示(ESNI)的IETF草案發佈剛剛1個月後[21]。另外,自2020年7月下旬起,ESNI協定也被封鎖[22][23]。
架構
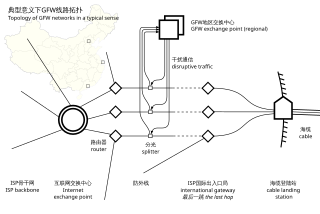
防火長城主要部署於北京、上海和廣州的三個大型互聯網交換中心,而非在國際出口[26][27],在省級部署的裝置較少[18]。根據「GFW技術評論」網站2010年的估計,其硬件組態如下[24][28]:
主要技術
深度包檢測(Deep packet inspection, DPI)是一種於應用層對網絡上載遞的資料進行偵測與處理的技術,被廣泛用於入侵檢測、流量分析及數據挖掘。就字面意思考慮,所謂「深度」是相對於普通的報文檢測而言的——相較普通的報文檢測,DPI可對報文內容和協定特徵進行檢測。
DPI是防火長城檢測關鍵詞及嗅探加密流量的基礎,藉助硬件設施、適宜的檢測模型和模式匹配演算法,它能夠精確且快速地從實時網絡環境中判別出目標流量,並作出審查者所期望的應對措施[29]。
被認為在防火長城部署了的深度包檢測包括:
- TLS協定。早期TLS版本中,伺服器握手響應,包括證書,是未被加密的,防火長城可以嗅探它而得知訪問站點,自TLS版本1.3開始,ServerHello之後的握手資訊,包括站點證書,也會被加密後傳輸,一般可以認為能防止對證書資訊的檢測[37][38];另外,SNI是TLS的一個擴充協定,該協定下,客戶端在握手過程開始時告訴伺服器其連接的域名,以便運作多個HTTPS網站的伺服器選擇並提供對應證書。而該擴充也未被加密[21]。基於UDP傳輸的QUIC的握手也使用TLS版本1.3,受上文所述的明文SNI影響[39];不過截至2025年4月[update],GFW在QUIC的域名封鎖列表和一般TLS並不一致[39][需要較佳來源]。
等待到深度包檢測章節中的「和處於域名黑名單中的相匹配」的域名後,防火長城會向查詢者注入虛假DNS回覆,比真的更早到達[40][31][41][42]。由於通常的域名查詢沒有任何認證機制,而且域名查詢通常基於的UDP協定是無連接不可靠的協定,查詢者無法驗證返回結果的正確性[42],客戶端接受其偽造回覆,並嘗試連接其中的IP,結果往往是逾時[31],或者出現無效TLS證書之警告。而其對TCP協定的查詢則使用TCP重設攻擊來阻止獲得任何正確結果[43][25]。

此種行為自2002年開始[19]以來有相當明確的特徵。
- 偽造回覆所包含的IP位址或者是保留地址、或者是固定中國境外IP集合中的一個[40],這些地址通常已經被封鎖[19][42][44]。
- 偽造回覆包有固定類型。一型的TTL值和IPID固定[44][45][46],每次注入出現1個[44];二型的TTL值周期性增加、IPID遞減[44][45][46],每次注入出現3個[44]。兩種類型都沒有設置「不分片」(Don't fragment)選項[44][45][46]。另外,2020年的研究指出有另一種新的IPID和TTL值都隨機,帶有「不分片」選項的回覆存在[46]。
這種注入是雙向的,不僅是在中國境內查詢境外DNS時、境外的DNS查詢途經中國時也會出現,這導致許多國外遞歸DNS伺服器的快取被污染[47]。
根據2014年的研究,防火長城的一個計算叢集有360個節點,每個節點的平均處理速度是每秒2800個DNS包[48][45]。
對於加密DNS,如DoT和DoH,防火長城使用基於IP埠和基於SNI的封鎖[49]。最早的封鎖針對Cloudflare提供的加密DNS服務,其一個IP位址1.1.1.1和域名cloudflare-dns.com在2020年末被發現封鎖[49]。
- 2010年3月,一名智利域名註冊商的技術人員稱,當用戶向的「I」根網域名稱伺服器的查詢facebook.com、youtube.com和twitter.com等域名時,返回的是虛假的IP位址,沒有轉到VeriSign公司執行的.com[50][51][52]。調查表明,由於錯誤的路由資訊,用戶的對此根伺服器的域名查詢被定向到一個中國的節點,「I」根伺服器運營商Netnod為解決問題,撤回了中國伺服器的路由通告,並聲稱自己的伺服器本身不包含任何錯誤路由,安全專家亦認為這次事件與Netnod無關,而是中國政府修改某處網絡時造成的[53][54]。4月,一家中國ISP的錯誤路由通告再次擴大了DNS污染對全世界的影響[55]。6月,匿名研究發現109個國家的三成遞歸DNS解析器受到防火長城污染[47],中國周邊地區如俄羅斯、東南亞最受影響[47][56]。Slashdot網友認為,中國的DNS污染是互聯網的真正威脅[56]。
- 2014年1月21日下午三點半,中國互聯網域名解析異常,大量網站被錯誤解析到IP位址
65.49.2.178,這個IP位於美國加利福尼亞州費利蒙市Hurricane Electric公司,被動態網公司租用於翻牆軟件連接節點[57][58]。動態網公司和研究人員認為這是因為防火長城的工作人員操作失誤[59][60][61],另一些人認為,不能排除真正的黑客借這一IP位址作為跳板發動攻擊的可能[62]。
重設(reset)是傳輸控制協定(TCP)的一種訊息,例如伺服器端在沒有客戶端請求的埠或者其它連接資訊不符時,系統的TCP協定堆疊就會給客戶端回覆一個重設通知訊息,該功能本來用於應對例如伺服器意外重新啟動等情況,而防火長城阻止TCP連接的技術實際上就是比連接雙方更快地傳送連接重設訊息,使連接雙方以為對方終止了連接[65]。
當GFW看到自客戶端傳送的第一個SYN包以啟動TCP三次握手時,其開始跟蹤該TCP連接的狀態。HTTP、SMTP、HTTPS等許多應用協定都基於TCP。GFW在該TCP控制塊(TCP control block)內進行上文所述之檢測[25][66],遇到預期關鍵字後,其會注入帶有一個RST選項的「一型」[已過時]和多個帶有RST/ACK選項的「二型」封包,這被認為是來自兩種同時部署的審查裝置。一型IPID為0,具有隨機的窗口尺寸,沒有設置「不分片」選項;二型則有周期性增加的TTL值和窗口尺寸,並且設置了「不分片」[67][25]。
有時防火長城在檢測到違禁關鍵字並注入一次重設後,會在固定時長內對具有相同三元組(客戶端IP、伺服器IP、伺服器埠)的連接不區分關鍵字違禁與否地持續注入[65][31][25],或者丟棄符合該三元組的封包[66],這被稱為殘餘審查(Residual censorship)[22][68]。前谷歌進階副總裁艾倫·尤斯塔斯曾發佈影片演示此種封鎖策略[69]。
防火長城主要採用路由擴散技術封鎖特定IP位址,也就是通過將需要攔截的IP位址組態為空路由、黑洞裝置或特別組態的自治系統上,在這些黑洞伺服器上可以什麼也不做,或者對這些報文進行分析和統計,取得更多的資訊,甚至可以做出虛假回應[70][71]。正常的情況下,靜態路由是由管理員根據網絡拓撲或是基於其它目的而給出的一條路由,所以這條路由是正確的情況下,可以引導路由器把報文轉發到正確的目的地。而防火長城的路由擴散技術中使用的靜態路由是一條有意組態錯誤的路由,其目的是為了把本來是發往某個IP位址的報文引導到一個「黑洞伺服器」上,而不是把它們轉發到正確目的地。通過動態路由協定的路由重分發功能,這些錯誤的路由資訊可以發佈到整個網絡[72]。
| “ | 在大規模自治域的出入口路由器上新接入一個起控管作用的子網絡或者AS域,將要受控的網絡地址組態在這個子網絡或者AS域內的路由器中,這樣利用動態路由協定的網絡拓撲自動辨識特性,在出入口路由器上將生成受控網絡地址的路由資訊,將自治域內聯網對這些受控網絡地址的訪問轉入到這個控管子網絡或者AS域的網絡中,從而實現對受控網絡地址的流量控制 。 | ” |
| ——《一種基於路由擴散的大規模網絡控管方法》[73] | ||
對於由使用虛擬主機服務供應商提供的多域名、單(同)IP的主機寄存服務的網站,如果封禁它的IP位址,就會造成「過度封鎖」(Overblocking):所有使用該供應商服務的、其他使用相同IP位址的網站也被封鎖,就算是「內容健康、政治無關」的網站,也不能倖免。其中的內容可能並無不當之處,但也不能在中國大陸正常訪問[65][74]。所以基於路由封鎖的方法現在主要用於針對自主擁有大量連續地址段的特定自治系統,例如Facebook,Google,Telegram,Twitter等;對於內容傳遞網路(CDN)的地址段可能不會採用這種地址封鎖的方法,以避免過度封鎖[75]。
因為有防火長城的存在,大量境外網站無法在中國大陸境內正常訪問,於是大陸網民開始逐步使用各類翻牆軟件突破防火長城的封鎖。針對網上各類突破防火長城的翻牆軟件,防火長城也在技術上做了應對措施以減弱翻牆軟件的穿透能力。通常的做法是利用上文介紹的各種封鎖技術以各種途徑打擊翻牆軟件,最大限度限制翻牆軟件的穿透和傳播。
2015年1月,部分國外VPN服務在中國大陸無法正常使用,包括L2TP/IPSec和PPTP協定。[76]
防火長城在2016年就能利用TLS的旁路泄露觀察封包特徵辨識TLS代理,研究人員利用隨機填充修改請求和握手中間傳送的封包大小,則可以正常瀏覽被審查的HTTP和HTTPS網站,關閉隨機填充丟包問題則會立即再現[77][78]。
自2021年11月初以來,防火長城部署了一種類似白名單的檢測方法:應用規則來豁免那些不太可能是完全加密的流量;然後它阻止其餘未被豁免的流量。由於翻牆軟件的流量多是完全加密的,這種方法十分有效,僅會誤傷大約0.6%的非翻牆互聯網流量[68]。

自2011年10月以來[79],防火長城通過主動探測(Active probing)[80]辨識翻牆伺服器,並隨後將其封鎖。其主要針對以下目標。
- 任何加密連接,包括SSH和Tor,並不針對特定協定。這是最早出現的探測。每當中國用戶嘗試加密連接,防火長城傳送「垃圾二進制(garbage binary)探針」[81][82],一系列偽亂數據,在建立加密連接前先訪問目標電腦,其目的在於在用戶建立加密連接前嗅探出他們所使用的反審查工具[79][83][82],任何從中國訪問境外HTTPS 443埠的連接都會在幾乎即時的情況下被刺探[81][82]。
- Tor。2011年10月起,防火長城的深度包檢測裝置已能辨識Tor指紋[81][84]。當中國的Tor客戶端試圖與境外Tor網橋建立連接,防火長城會在每15分鐘周期(如15分鐘後,30分鐘後)內傳送探針會嘗試與Tor進行SSL協商和重協商,但目的不是建立Tor連接[79],每次探測持續3分鐘[84][35]。這種探測還會在春節等假期期間停止[84][35]。而2015年的研究指出,防火長城已經可以即時主動探測Tor網橋,而不是每15分鐘執行一次[85]。被探測的網橋類型包括obfs2和obfs3等[86][85]。
- SoftEther VPN。2015年9月發現[85][87]。起初使用固定的IP,如
210.72.128.200,被封鎖之後使用亞馬遜EC2等雲服務發起探測,模仿SoftEther的客戶端握手去辨識有效的SoftEther的IP[88]。
- Shadowsocks。可能是從2019年5月開始的[89][90]。
2011年3月,防火長城曾經對Google部分伺服器的IP位址實施自動封鎖(按時間段)某些埠,按時段對www.google.com(用戶登入所有Google服務時需此域名加密驗證)和mail.google.com的幾十個IP位址的443埠實施自動封鎖,具體是每10或15分鐘可以連通,接着斷開,10或15分鐘後再連通,再斷開,如此循環,使中國大陸用戶和Google主機之間的連接出現間歇性中斷,使其各項加密服務出現問題。[91]Google指責中國這樣的封鎖手法,因為Gmail並非被完全阻斷,營造出Google服務「不穩定」的假象,表面看起來好像問題出自Google本身。[92]
2014年5月27日起,Gmail網頁版的80和443埠被封鎖。2014年12月26日起,Gmail客戶端所用的IMAP/SMTP/POP3埠也被封鎖。[93]
2011年5月,中國大陸境內很多互聯網公司以及高校、學院、科研單位的對外網絡連接都出現問題,包括中國科學院。當時有分析指斷網可能是因為防火長城已經具有了探測和分析大量加密流量並對用戶IP位址執行封鎖的能力,而各大機構的出口被封也在其中。具體表現為:當用戶使用了破網(翻牆)軟件後,其所在的公共網絡IP位址會被臨時封鎖,所有的國際網站都無法訪問,包括MSN、iTunes Store等,而訪問國內網站卻正常,但如果使用境外的DNS解析域名則將會由於DNS伺服器被封鎖導致無法解析任何域名,國內網站也會無法打開[95]。自由亞洲電台引述業內人士分析指,此舉是中國當局在測試逐步切斷大部分人訪問國際網站的措施,以試探用戶反應並最終達到推行網絡「白名單」制,也就是凡沒有在名單上的企業或團體其網絡域名將不能解析,一般用戶也無法訪問[96]。而中共黨機關報《人民日報》旗下的《環球時報》英文版則引述方濱興指,一些ISP必須為自己的用戶支付國際流量費用,因此這些公司「有動機」去阻礙用戶訪問國外網站。一位不願留名的工信部官員說,用戶碰到這些情況應先檢查自己和網站的技術問題。[97][98]
2013年1月26日,有中國大陸的用戶在訪問GitHub時發現證書無效,經檢查發現,其的證書變為了一自簽署的X.509證書,生成時間為2013年1月25日,有效期一年,故有人推測GitHub疑似遭到了中間人攻擊。 GreatFire和研究人員認為攻擊是由中國政府策劃的[99]。
自2014年8月28日起,原先可以通過IPv6直連Google的中國教育網(CERNET)內試圖通過HTTPS連接*.google.com.*等網頁時,可能收到TLS證書錯誤的提示,其中以連接www.google.com.hk幾乎是每次連接均收到攻擊,而其它連接例如ipv6.google.com和accounts.google.com也有受到攻擊的報告,但攻擊發生的概率相對較低。偽造的TLS證書顯示其為google.com,頒發機構即為其本身,與真正的證書不同,顯示谷歌在中國教育網上受到中間人攻擊。
2015年1月17日,Outlook遭到了中間人攻擊[100][101]。19日,GreatFire撰文稱懷疑此攻擊是由網信辦發起的[102];22日,網信辦對此文作出了回應,稱「Greatfire.org是境外反華組織創辦的反華網站」,「這一無端臆測,純屬境外反華勢力的造謠和污衊」[103]。
正常情況下,郵件伺服器之間傳輸郵件或者數據不會進行加密,故防火長城能輕易過濾進出境內外的大部分郵件,當發現關鍵字後會通過偽造RST封包阻斷連接。而因為這通常都發生在數據傳輸中間,所以會干擾到內容[36]。也有網友根據防火長城會過濾進出境郵件的特性,尋找到防火長城部署的位置[104]。
2007年7月,大量使用中國國內郵件服務商的用戶與國外通訊出現了退信、丟信等普遍現象[105]。表現為[106]:
- 中國國內郵箱給國外域發信收到退信,退信提示
Remote host said: 551 User not local; please try <forward-path>或者Connected to *.*.*.* but connection died.(#4.4.2) - 中國國內郵箱用戶給國外域發信,對方收到郵件時內容均為
aaazzzaaazzzaaazzzaaazzzaaazzz - 國外域給中國國內郵箱發信時收到退信,退信提示
Remote host said: 551 User not local; please try <forward-path> - 國外域給中國國內郵箱發信後,中國國內郵箱用戶收到的郵件內容均為
aaazzzaaazzzaaazzzaaazzzaaazzz
對此,新浪的解釋是「近期互聯網國際線路出口不穩定」;而萬網客戶服務中心的解釋是「近期國內互聯網國際出口存在未知的技術問題」[107]。而網民普遍認為這與防火長城有關[105]。
2014年12月26日,有很多中國大陸網民反映說一度無法通過客戶端登入到Gmail。在此之前,國內一些用戶可以通過IMAP、SMTP和POP3接收、下載郵件;據路透社報道谷歌旗下的Gmail業務已經被當局封鎖。[108]12月30日,Gmail的郵件伺服器已在中國大陸境內恢復部分功能。[109][110]但Gmail網頁版至今仍被封鎖。
參與建設

中國工程院院士、北京郵電大學前校長方濱興是防火長城關鍵部分的首要設計師[2][111][112][113],被稱為「中國國家防火牆之父」[114][111]。
思科系統和一些其他西方通訊裝置供應商向中華人民共和國政府提供了具有流量監控和過濾功能的互聯網裝置,用來封堵網站和追蹤網上一些活躍的持不同政見者[115][116]。2006年2月,美國國會為此召開聽證會,向思科、微軟、雅虎、Google四家公司提出質詢[117]。美國中國資訊中心(China Information Center)的吳弘達指責,思科不斷主動地與中國中央及各省國家安全部門聯絡,向其提供最新技術,包括警車間的即時通訊和指揮系統、以及聲音辨識技術和指紋鑑別技術[117]。記者Sarah Lai Stirland在Wired News發表了一篇文章,並公佈了一份泄漏的思科機密幻燈片文件。該文件詳細描述了思科和中國政府在金盾工程上具有商業性質的合作[118]。她還在文章中指責,思科在市場行銷中將這些技術明確劃分為「鎮壓工具(A Tool of Repression)」。思科的辯護者聲稱,實際上,在中國大陸現行的內容過濾系統中,路由器只是作為底層執行裝置對人為指定的目的地址進行封鎖,這是任何一台商用路由器都必須提供的基本功能,思科並沒有向中國政府提供特別開發和客製化的互聯網裝置[119][31]。
奇虎360公司曾經加入中國GFW防火長城計劃,並早在2005年,奇虎360就已經特派兩位高管齊向東、石曉虹加入研究搜尋引擎安全管理系統,助力該專案的實行。奇虎360方面拒絕透露其在GFW防火長城計劃中承擔的任務與角色,但從2012年7月獲得的一份資料來看,該專案落實在北京三際無限網絡科技有限公司,主要完成人里除了方濱興在列,時任奇虎360高管齊向東(奇安信的建立者)與石曉虹也名列其中[120][121]。2012年7月,該公司董事長周鴻禕在新浪微博否認相關報導[122]。
2012年,中國互聯網專家毛向輝透露,方濱興本人已經不再直接負責中國政府防火長城專案,其已經交給一家叫啟明星辰的技術公司和一些管理成熟的團隊[123][124][9],該公司也創立於1996年[124]。
相關報道
2007年,人民網轉載了題為「百度日本站被GFW封鎖 疑與色情內容有關」的文章,是官方最早先提到此系統的報道之一。[125]2011年2月17日有記者在中國外交部新聞發佈會上問及互聯網封鎖等問題,發言人馬朝旭的回答是:
中國政府...依法保障公民言論自由,包括網上言論自由。同時,中國對互聯網依法進行管理,這符合國際慣例。我們...反對任何國家藉口互聯網自由等問題干涉中國內政。[126]
次日,方濱興在接受《環球時報》英文版採訪時被問及防火長城是如何運作的,他拒絕回答,說這是機密(It's confidential)[114][111]。
2014年12月,中共黨刊《紅旗文稿》建議當局繼續改進和完善網絡監管措施,構築高效的「過濾網」和「防火牆」,同時要斬斷「翻牆軟件」傳播的利益鏈條[127][128]。
評價
防火長城對網絡內容的審查是否限制和違反了言論自由,一直是受爭議的話題[129],官方說辭也相當籠統[126][130]。
2007年有報告認為,防火長城並非防火牆,而是一種圓形監獄,其審查即使能輕易繞過,也會促使人民自我審查[131]。
美國貿易代表辦公室在2016年4月發佈的有關貿易環境的年度報告中稱,中國對互聯網的審查過濾對外國企業是嚴重的貿易障礙。報告指出,中國對很多境外網站的封鎖都很武斷,有些和社會穩定或國家安全沒有關係的網站也被封鎖,比如美國一家家居裝飾網站,其內容都毫不敏感,卻是典型的、有可能被防火長城封鎖的網站[132][133][134]。對此,中國外交部發言人洪磊回應:「我們希望各國尊重其他國家自主選擇的互聯網發展道路、管理模式、公共政策以及參與互聯網治理的權利」[130][135];《環球時報》為此發表社評,認為美國同樣有大量貿易壁壘,並表示「網絡防火牆」重新鞏固了互聯網時代中國主權受到侵蝕的部分,遏制西方意識形態滲透,幫助中國更加強大,其必將得到歷史的正面評價[136]。
北京大學和史丹福大學兩名經濟學家在2018年的研究發現,中國大學生對於獲取未經審查的政治敏感資訊漠不關心。他們認為,審查制度十分有效,不僅敏感資訊難以取得,民眾逐漸也不要求取得它們[137]。
2021年11月,網信辦發佈的《網絡數據安全管理條例(徵求意見稿)》寫道:數據跨境安全網關是指「阻斷訪問境外反動網站和有害資訊、防止來自境外的網絡攻擊、管控跨境網絡數據傳輸、防範偵查打擊跨境網絡犯罪的重要安全基礎設施」[4]。
影響
相關事件
參見
- 大炮(Great Canon)
註釋
參考來源
外部連結
Wikiwand - on
Seamless Wikipedia browsing. On steroids.



